Integrating with PingOne
![]()
![]()
![]()
Before starting the integration process, you must have requested, and been approved for, an Onshape Enterprise account or trial, and have an Onshape Enterprise domain name.
An example of an Enterprise domain name might be: MyCompanyName.onshape.com.
You can use only one (single sign-on) SSO provider at a time.
This configuration process might fail without parameter values customized for your organization. Use your PingOne single sign-on dashboard to add Onshape as an application and record the values that are specific for your organization. You need those values for the following procedure.
Onshape signs all outgoing SAML certification requests. You are not required to upload any certificates (for example, a SAML signing certificate), except in the case of ADFS integration because ADFS validates incoming SAML requests.
Add Onshape to your PingOne single sign-on account
To enable single sign-on for your company, you must first add the Onshape application to your PingOne single sign-on account:
-
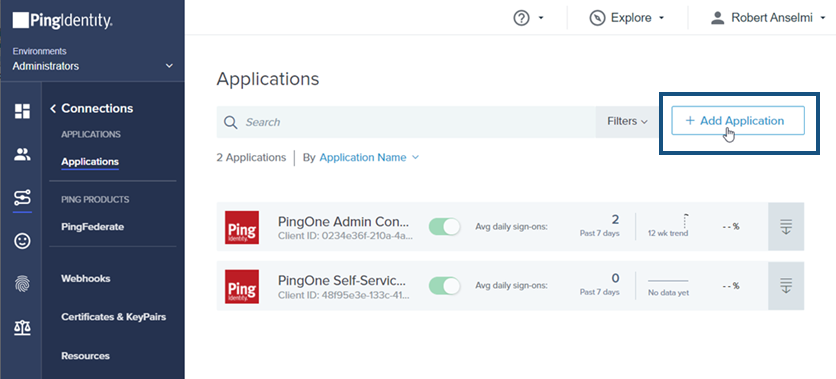
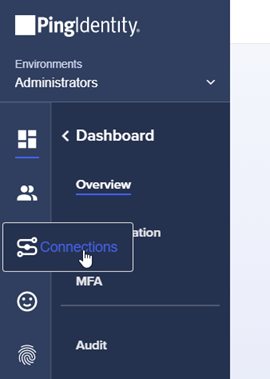
Sign in to the PingOne portal as an Administrator. Click the Connections icon on the left side navigation pane.
-
Click Add Application.
-
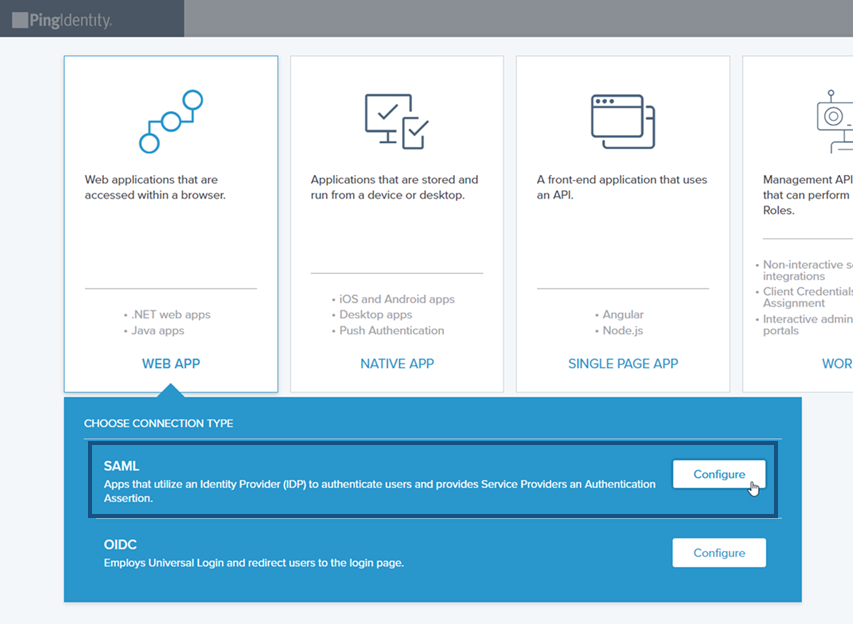
Click the Web App box. Then click the Configure button to the right of the SAML connection type.
-
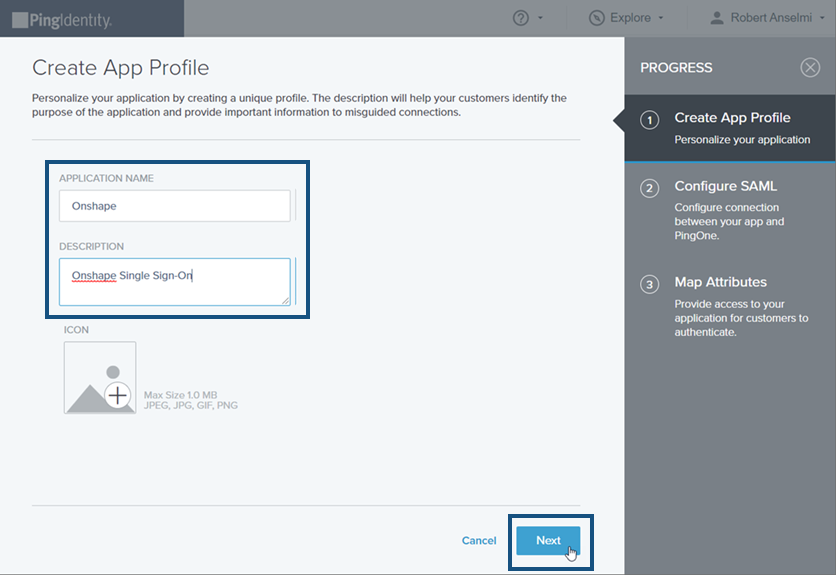
In the Create App Profile tab that opens, enter an Application Name and Description. Then click the Next button at the bottom of the pane.
-
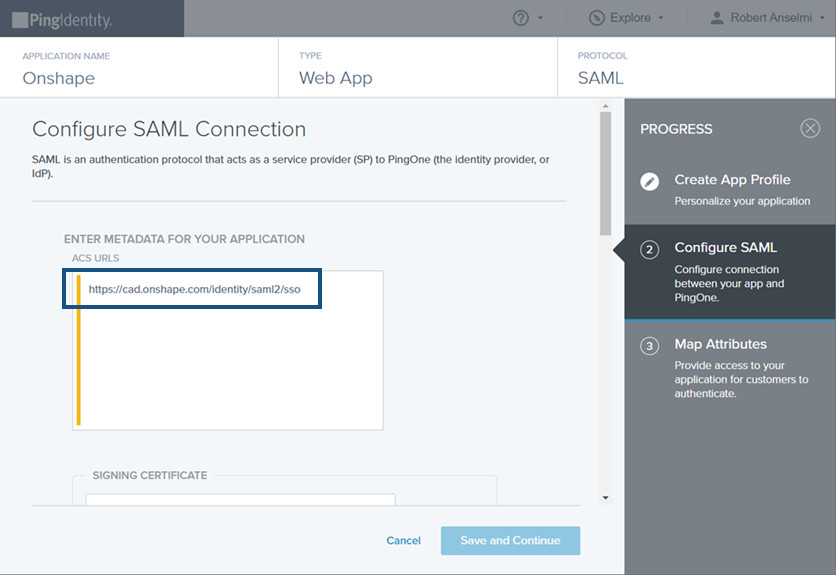
In the Configure SAML tab that opens, enter https://cad.onshape.com/identity/saml2/sso in the ACS URL field.
-
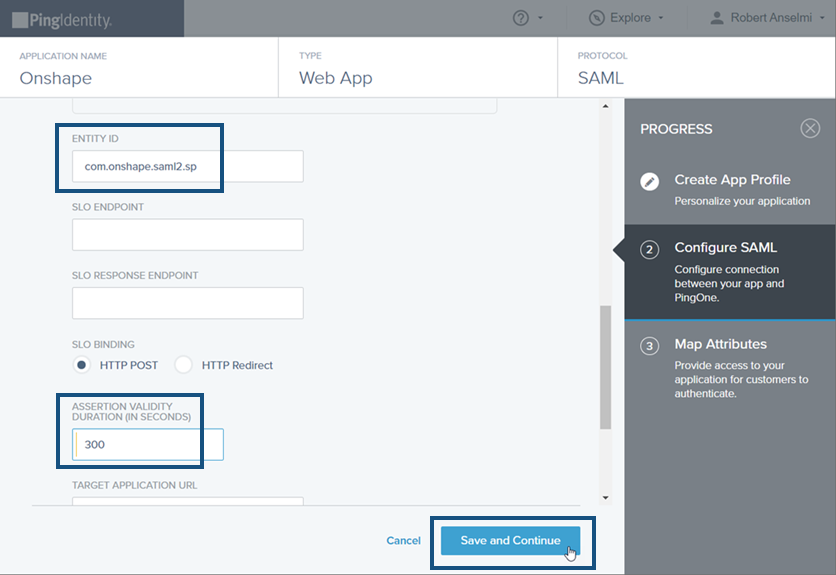
In the same tab, scroll down and enter com.onshape.saml2.sp In the Entity ID field, and 300 In the Assertion Validity Duration in Seconds field. Then click the Save and Continue button.
-
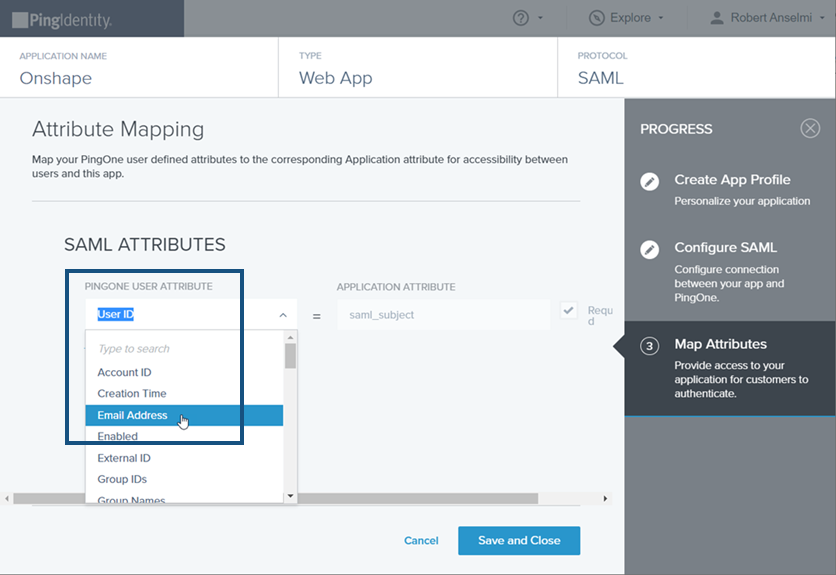
In the Map Attributes tab, select Email Address from the PingOne User Attribute drop-down list.
-
In the same tab, create the following three SAML Attributes:
-
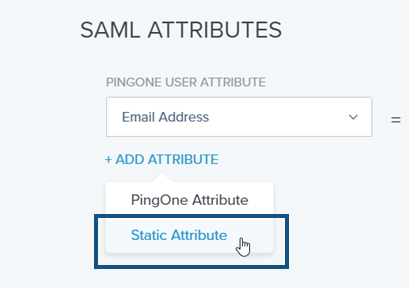
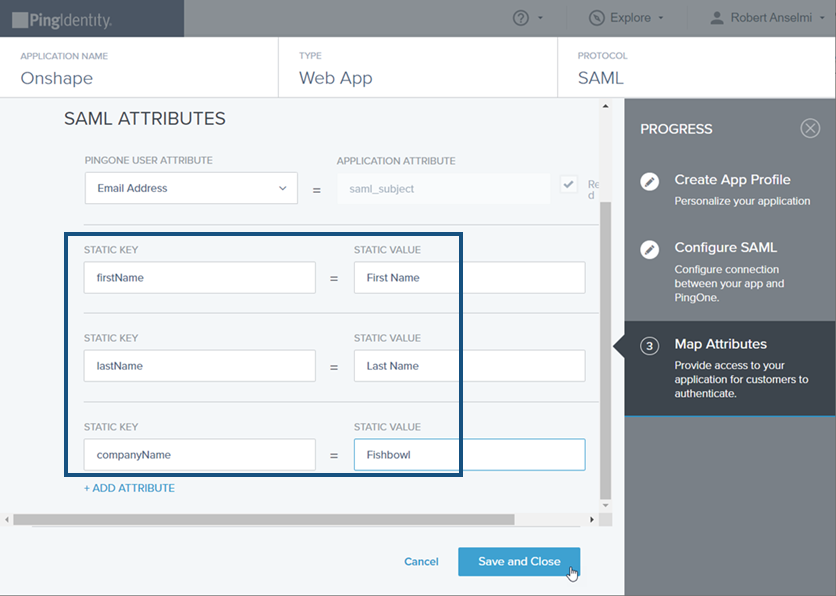
Click the Add Attribute link and select Static Attribute from the drop-down list. This creates the first Static Attribute. In the Static Key field, enter firstName, and in the Static Value field enter First Name.
-
Click the Add Attribute link again, and select Static Attribute from the drop-down list. This creates the second Static Attribute. In the Static Key field, enter lastName, and in the Static Value field enter Last Name.
-
Click the Add Attribute link again, and select Static Attribute from the drop-down list. This creates the third Static Attribute. In the Static Key field, enter companyName, and in the Static Value field enter your domain name prefix. For example, if your Onshape enterprise name is Fishbowl.onshape.com, enter Fishbowl into the field.
-
-
Once all three SAML Attributes are entered, it should look similar to the image below. Click the Save and Close button.
-
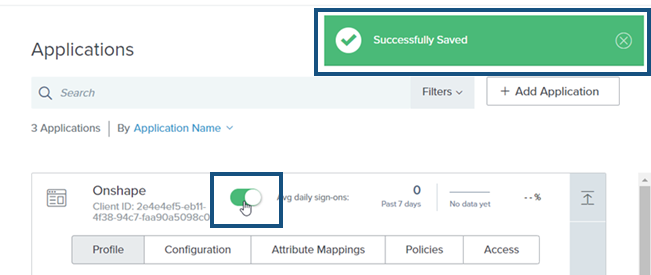
The Applications window opens. Click the Avg daily sign-ons switch to enable sign-ons to the application. A notice appears at the top right corner stating that the application is Successfully Saved.
-
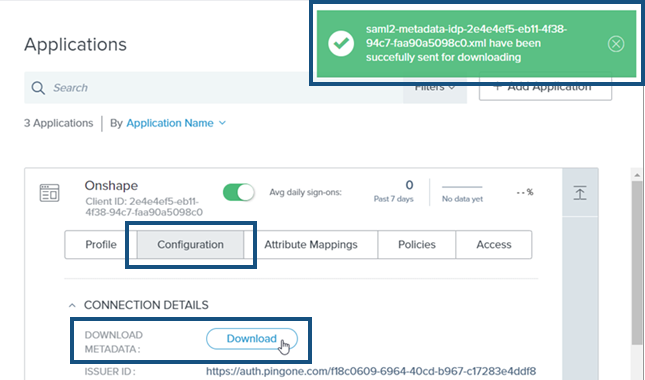
Click the Configuration subsection. Then click the Download button to download the metadata file. A message appears in the top right upon successful download of this file. Click X to dismiss the message.
The ACS URL, above, must be "cad.onshape.com" and not the URL of your Onshape enterprise.
Upload the metadata configuration file in Onshape
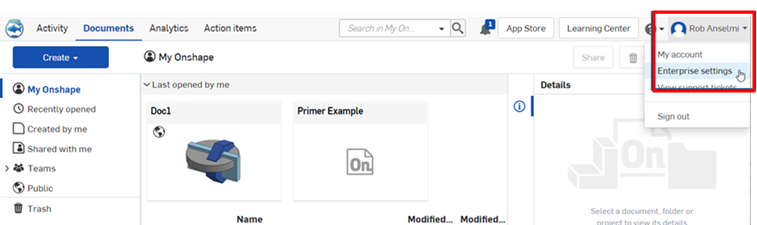
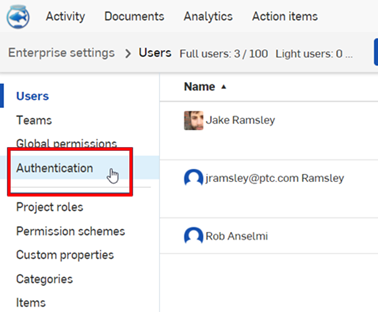
- Sign in to your Onshape enterprise account, using your specialized domain name, as an administrator.
Select
Enterprise settings
from your account.
- Select
Authentication
from the left navigation menu.
-
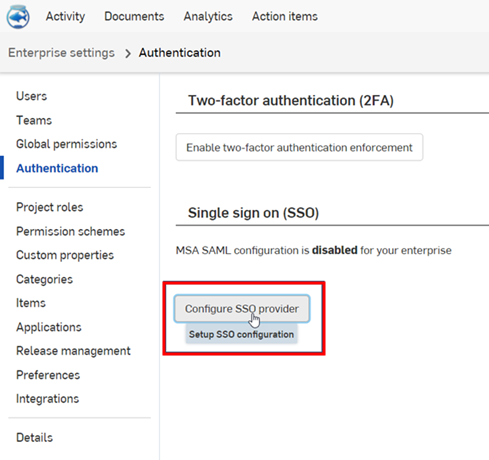
In the Single sign-on (SSO) subsection, click the Configure SSO provider button.
-
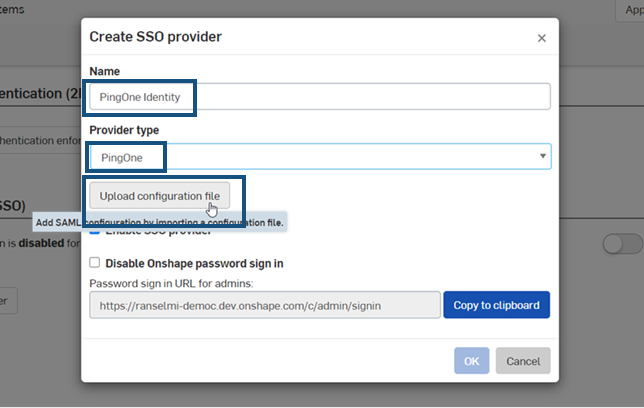
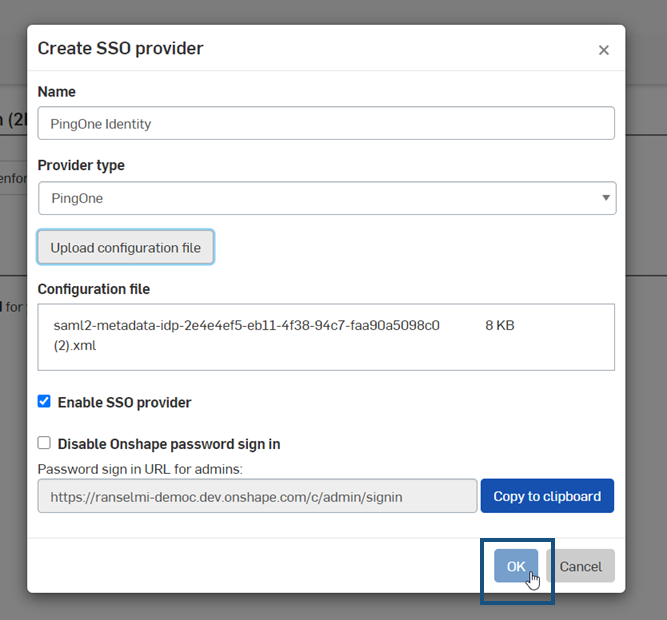
The Create SSO provider dialog opens. In the Name field, enter name, such as PingOne Identity. In the Provider type drop-down, select PingOne. Then click the Upload configuration file button.
-
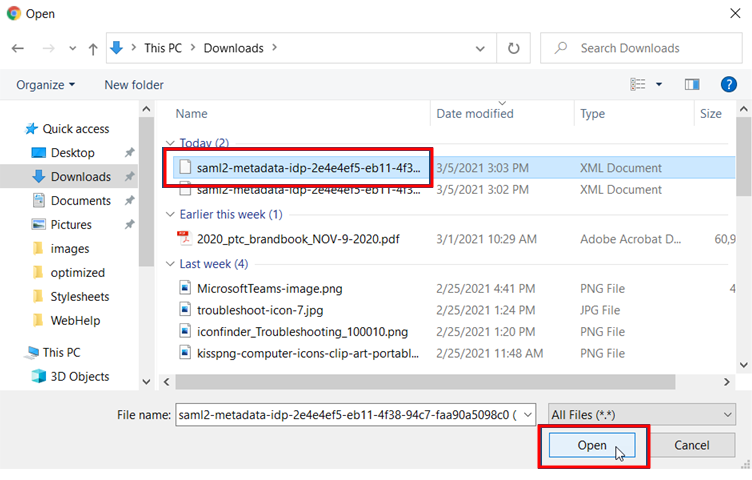
Locate and select the metadata configuration file you downloaded previously, and click Open.
-
Click OK.
-
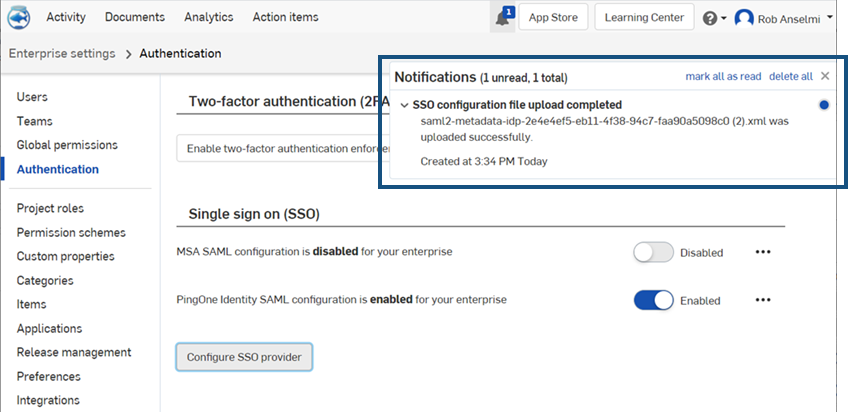
The file is uploaded. A notification appears when the upload is completed.
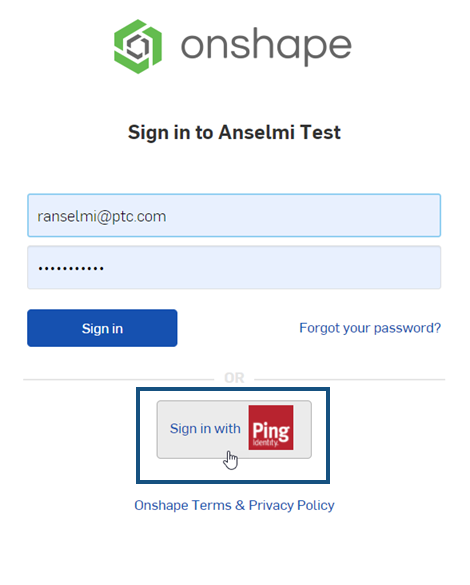
- Sign out of both your Onshape and PingOne accounts. Be sure to do a hard refresh of both accounts. When you reach the Onshape sign-in page once again, the page has a new
Sign in
link at the bottom, for your Single sign-on provider.
You can disable the typical Onshape password sign-in for your users and show only the SSO provider sign-in prompt for the Onshape URL. However, do not perform this step at this time. Make sure you can sign in to Onshape yourself (as administrator) before disabling this additional sign-in option. You can return here later, once you verify you can sign in through your SSO provider.
Choosing to enforce signing in to Onshape via SSO also results in users not being able to sign in to non-enterprise domains directly, such as cad.onshape.com.